A new threat to your computers can be contracted simply by visiting certain high-profile sites. Through a technique known as “malvertising,” banner ads are being used to spread a form of malware known as ransomware. In this case, CryptoWall 2.0, on such prominent Web sites as Yahoo, AOL, Match.com, The Atlantic, and MajorLeagueBaseball.com.
The websites themselves aren’t to blame. Rather these virulent ads are processed through advertising networks, including Rubicon Project, OpenX, and Right Media/Yahoo advertising, which have failed to carry out adequate checks for malicious content. CryptoWall 2.0 encrypts all the files on the hard drive on a victim’s computer and any attached network drives.
If the victim doesn’t pay a ransom by a deadline, those files are lost. Frequently the only way someone will know they have been infected will be telltale files in each directory titled “Decrypt_Instructions.” The latest version is memory resident, meaning it never installs on the hard drive but just runs in memory and disappears when the machine is shut down while the encrypted files remain.
An estimated 3 million people have been exposed to the malvertisements since the campaign was first detected in mid-September. The CryptoWall criminals earn an estimated $25,000 a day from this attack, using a complex bitcoin laundering method to hide their profits. An estimated one billion Android smartphones and tablets may be the next target as a version of the ransomware go on sale in underground web forums.
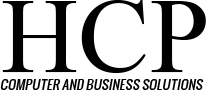
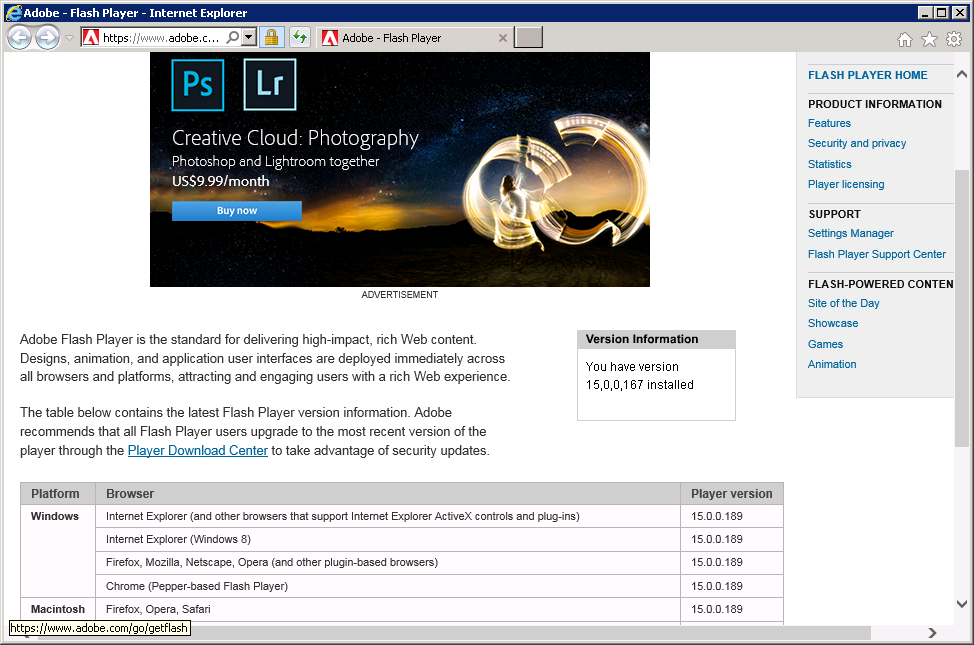
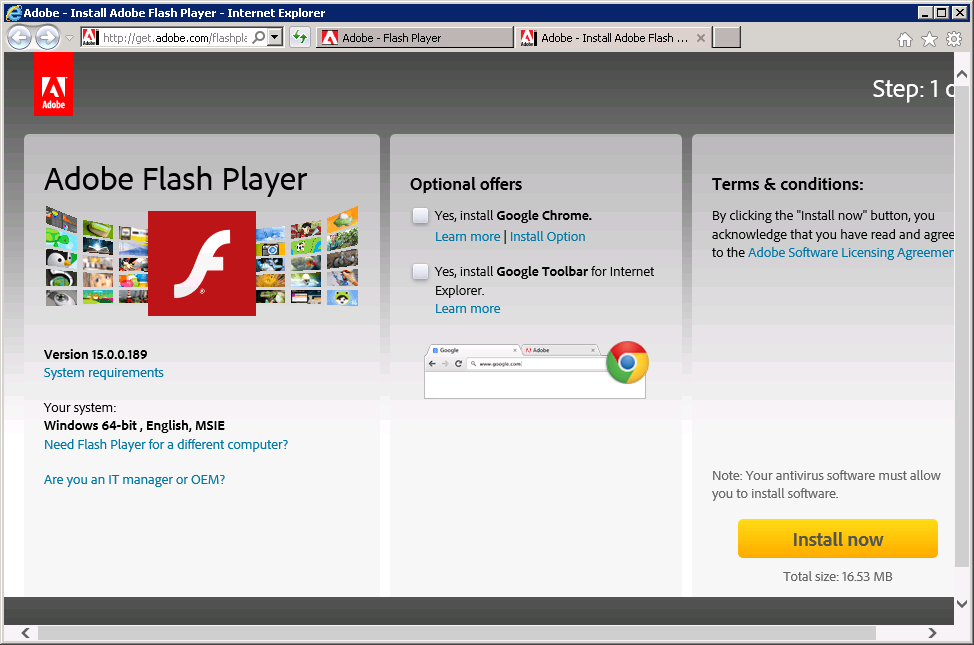
CryptoWall gets into the computer through a security vulnerability in Adobe Flash Player. Your options to protect your data are either to update to the latest version of Flash. Please see the directions in a recent blog entry or remove Flash from your computer altogether.
Firefox offers a plug-in called Ghostery that blocks third-party ads and trackers from loading when a site is launched. Chrome has a similar extension called AdRemover. Also, always back up your data on an external hard drive, either of your own that you disconnect after you back up, or it may get encrypted too, or a remote one (“the Cloud”).
If you are concerned that your system may be infected, please submit a request. We will be happy to help. Stay safe!